API Security: Best Practices for API Activity Data Acquisition
Blog Blog https://www.akamai.com/blog CySecBot CySecBot
More results...
Blog Blog https://www.akamai.com/blog CySecBot CySecBot
Blog Blog https://www.akamai.com/blog CySecBot CySecBot
Whether you are moving to a new neighborhood, considering opening a business in your current state or a different one, or considering opening a business in a specific area, it’s essential to research crime data. Crime is always a concern, and understanding the crime of your intended neighborhood can make or break your final decision. […]
Over 350 million individuals were impacted by data breaches in the US in 2023 and 11% of all publicly traded companies have been compromised
Southern Water confirmed a data breach had occurred after the Black Basta ransomware group purportedly published personal information held by the firm
Blindly trusting your partners and suppliers on their security posture is not sustainable – it’s time to take control through effective supplier risk management
Criminals can now deploy phishing sites on any type of web server, even when commonly used server-side technologies such as PHP are not supported.
Phishing kits are predominantly implemented in PHP, as this provides the server-side functionality required to store and transmit stolen credentials without publicly revealing where they are being sent.
PHP is a widely used platform and is often supported on low-cost or compromised hosting platforms. Consequently, very few phishing kits are implemented in any other server-side language. For example, only a very small number of phishing kits have even been written in ASP.NET to run on Microsoft web servers.
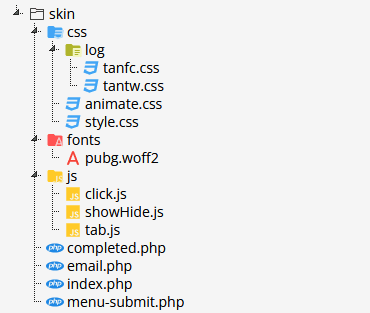
An example of a typical phishing kit. It contains server-side PHP scripts, plus other resources such as fonts, stylesheets, and client-side JavaScript files.
We also see relatively small numbers of kits that do not contain any server-side scripts but do still rely on a PHP script to ultimately process their stolen data. These kits use static HTML pages to impersonate the targeted organisation, with web forms that submit stolen credentials directly from the victim’s browser to a PHP script hosted on a central remote “dropsite”. The PHP script then logs or forwards the stolen credentials to the criminal, typically via email, Telegram or Discord.
However, some recent phishing kits have gone one step further and eliminated the need for PHP scripts anywhere along the chain, thus eliminating a single point of failure that is inherent when hosting your own dropsite.
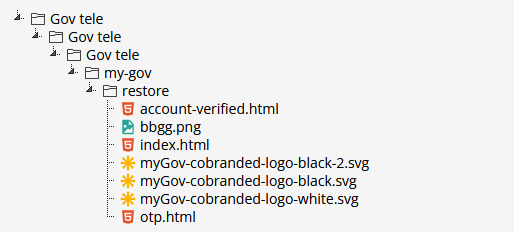
An example of a PHP-less phishing kit. It contains only images and static HTML pages which submit stolen credentials directly from the victim’s browser to a Telegram chat.
These new kits expand the range of hosting options open to the phisher, as they can be deployed on any static content hosting platform, regardless of what operating system it’s …
The Zero Day Initiative’s first Pwn2Own Automotive competition has handed out over $1m for 24 zero-days
Kaspersky experts review their privacy predictions for 2023 and last year’s trends, and try to predict what privacy concerns and solutions are to come in 2024.
Hewlett Packard Enterprise reveals that Russian state APT29 hackers stole data from corporate mailboxes