A Report Template for Incident Response
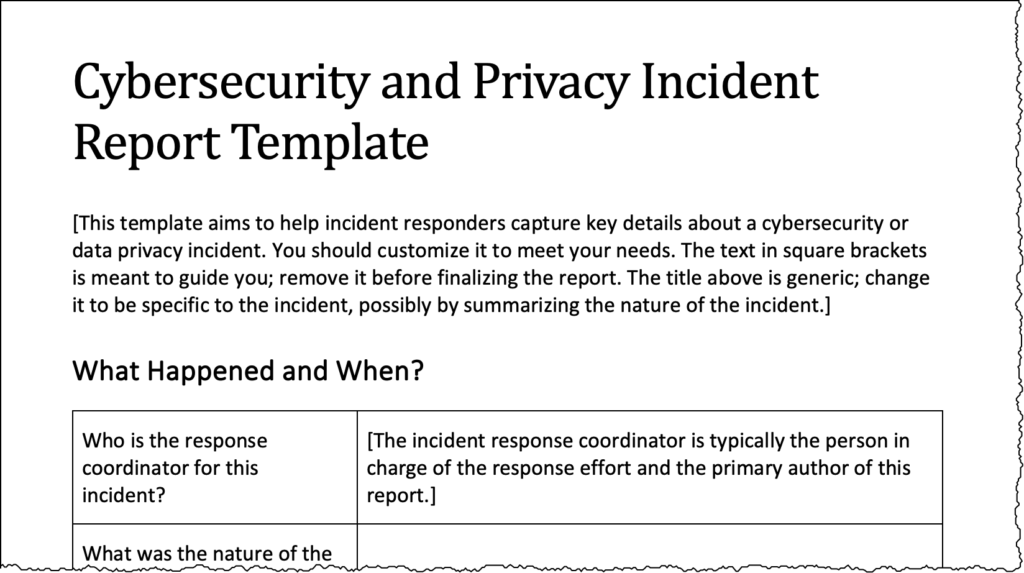 Preparing for cybersecurity and data privacy incidents involves creating checklists and documented plans to enable the response team to do their best during the incident. Preparation also includes creating a template that the team can use as the basis for the incident report, which is critical to ensuring that the incident is handled well. We…
Preparing for cybersecurity and data privacy incidents involves creating checklists and documented plans to enable the response team to do their best during the incident. Preparation also includes creating a template that the team can use as the basis for the incident report, which is critical to ensuring that the incident is handled well. We…
 As companies seek to optimize operations and constrain expenses, cybersecurity leaders worry about funding the projects we consider essential. Fortunately, in such an economic climate, we can achieve an outcome that benefits the organization from cybersecurity as well as financial perspectives. Here’s how. Start by critically reviewing how you’ll spend the security funds; this involves…
As companies seek to optimize operations and constrain expenses, cybersecurity leaders worry about funding the projects we consider essential. Fortunately, in such an economic climate, we can achieve an outcome that benefits the organization from cybersecurity as well as financial perspectives. Here’s how. Start by critically reviewing how you’ll spend the security funds; this involves…  Despite years of public shaming by security professionals, some SaaS vendors only offer Single Sign-On (SSO) in high-end “enterprise” product tiers. By withholding this capability from smaller organizations, they put customers’ security at risk. Moreover, they base a pricing strategy on a weak signal and miss an opportunity to lower their own security risk. Charging…
Despite years of public shaming by security professionals, some SaaS vendors only offer Single Sign-On (SSO) in high-end “enterprise” product tiers. By withholding this capability from smaller organizations, they put customers’ security at risk. Moreover, they base a pricing strategy on a weak signal and miss an opportunity to lower their own security risk. Charging…  Today’s CISOs are more than technologists—we strive to make ourselves well-rounded business leaders. This involves aligning our efforts with business objectives and collaborating with colleagues who are not experts in IT or security. In fact, Gartner’s research found that top-performing CISOs regularly meet with three times as many non-IT stakeholders as they do with IT…
Today’s CISOs are more than technologists—we strive to make ourselves well-rounded business leaders. This involves aligning our efforts with business objectives and collaborating with colleagues who are not experts in IT or security. In fact, Gartner’s research found that top-performing CISOs regularly meet with three times as many non-IT stakeholders as they do with IT…  Too many people are unsure how to enter or grow in the cybersecurity industry. It’s a relatively young field, and we haven’t done a good job of defining what it means to have a career in it. Hiring managers who are worried about finding candidates because of the much-discussed cybersecurity skills gap should consider the…
Too many people are unsure how to enter or grow in the cybersecurity industry. It’s a relatively young field, and we haven’t done a good job of defining what it means to have a career in it. Hiring managers who are worried about finding candidates because of the much-discussed cybersecurity skills gap should consider the…  When contemplating the next step in your career as a cybersecurity leader, understand what you do best and what you enjoy doing. Figuring this out will help you identify organizations and projects that will benefit from your superpowers and accelerate your growth as a professional. As an added bonus, you’ll be more effective in communicating…
When contemplating the next step in your career as a cybersecurity leader, understand what you do best and what you enjoy doing. Figuring this out will help you identify organizations and projects that will benefit from your superpowers and accelerate your growth as a professional. As an added bonus, you’ll be more effective in communicating…