Ransomware Payments Hit a Record $1.1 Billion in 2023
After a slowdown in payments to ransomware gangs in 2022, last year saw total ransom payouts jump to their highest level yet, according to a new report from crypto-tracing firm Chainalysis.
More results...
After a slowdown in payments to ransomware gangs in 2022, last year saw total ransom payouts jump to their highest level yet, according to a new report from crypto-tracing firm Chainalysis.
Blog Blog https://www.akamai.com/blog CySecBot CySecBot
2/7/24 National Security and Korean News and Commentary
Access National Security News HERE.
Access Korean News HERE.
National Security News Content:
1. Opinion | What a Russian and Ukrainian general agree on: This battlespace is differe…
The maintainers of shim have released version 15.8 to address six security flaws, including a critical bug that could pave the way for remote code execution under specific circumstances.
Tracked as CVE-2023-40547 (CVSS score: 9.8), …
AnyDesk confirmed recently that a cyberattack has affected their product systems. The hackers accessed the source code and private code signing keys. Initially, the 170,000 customers remote access software company claimed an unplanned maintenance to ex…
“You’d have an incomprehensible level of computational, predictive, analytic, and psychic skill. You’d have the mind of God.” An exclusive excerpt from 2054: A Novel.
Most online users have experienced it. You do an online search for healthcare purposes, travel information, or something to buy and soon you’re being bombarded with emails and targeted online ads for everything related to your search. That’s because…
2024 will be the year of the vCISO. An incredible 45% of MSPs and MSSPs are planning to start offering vCISO services in 2024. As an MSP/MSSP providing vCISO services, you own the organization’s cybersecurity infrastructure and strategy. But …
Seafarer’s Companion: More than just internet. It’s crew welfare, reimagined. Ditch the spotty signal and upgrade to seamless connectivity with Starlink & 5G. This all-in-one solution goes beyond internet access, offering dedicated hardware, softw…
Netcraft has recently observed that criminals abused SendGrid’s services to launch a phishing campaign impersonating SendGrid itself. The well-known provider, now owned by Twilio, makes sending emails at scale simple and flexible. In addition to scale, the promise of high deliverability and feature-rich tools make Sendgrid a sought-after service for legitimate businesses and a likely target for criminals.
The campaign observed uses a variety of complex lures, such as claiming the victim’s account has been suspended while its sending practices are reviewed or that the victim’s account is marked for removal due to a recent payment failure, combined with other SendGrid features to mask the actual destination of any malicious links.
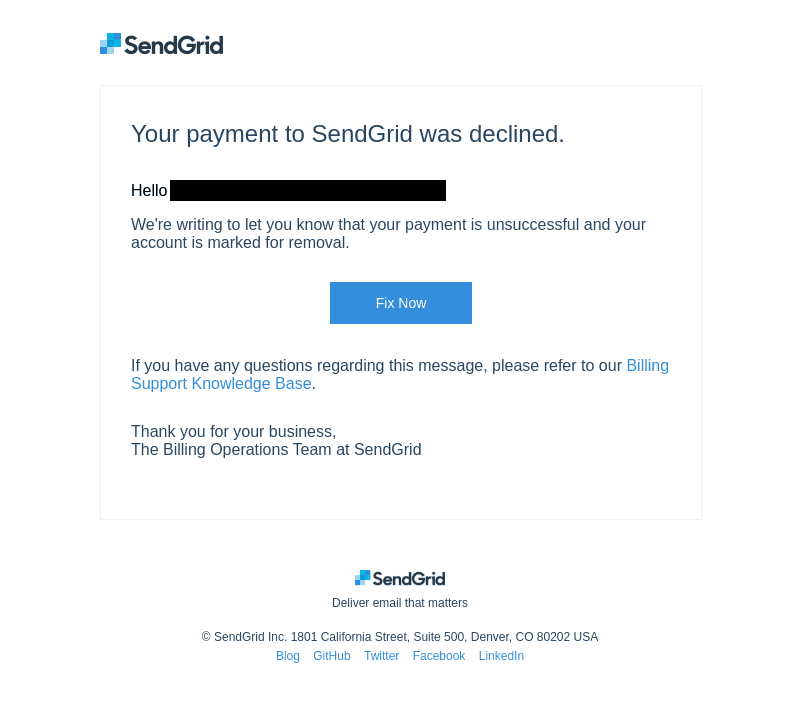
Screenshot of one of the phishing emails seen by Netcraft in the campaign.
The criminals behind the campaign used SendGrid’s click-tracking feature, with the malicious link masked behind a tracking link hosted by SendGrid. As the actual destination link is encoded in a URL parameter, even technically savvy recipients cannot determine its destination without following it.
https://u684436[.]ct[.]sendgrid.net/ls/click?upn=MlKqR181cN-2FwVofVyYroZohPHYCFmcOANwhWCUdTCBwPOc8txaiCuzTlogC05KN3LNFQ-2BuY0GGAqsU1nral07J5ZAzdZaZBAuJ7sV0-2BXHfumQD5I7-2FksS6M-2Bkp-2BkG47JcUbzDR8JwfwRM53-2BjxY8Q39KSfdEFQ9435uyTBM5TtspkyY3jUnvibv5C-2BopzMIluG2QhFh3lCZT2E5thEQQlvnZzjigw0zd2QIpDJ1mDMyGAOP9FKPeH-2BubdRj8uMW7TYzi-2FryttpaWt-2FacBOIgmTucX37Bpzwo8hDwYWOfxtiszu0DQpSrDO3oXpdkl-2B4s7wZAW0B-2FGDFBUzYJTXj74HRI9K2dpGobo82sm-2BazB2pF4rB-2BmwcxWwFL-2FpuLyZHB39O28qMVDOVLLbjWvpdUCCWXeMbVjwqJJJ-2FJJcfiX9cVoMVr52N2vZshdxGLBhIHeg5gMDA8qUev9sXguFrcp8VNlV-2FhMxARF1RUvbSCJCUd-2Faf2xJXq65WP0ikjyx7BLg1hmUr3QcV9IstauGE08g-3D-3DmcLN_IrVKFt61B0RSPoIcLeWyNg52nFk05lKq9QPi-2FlqEDp6KgcjnqupRcHzKcBBn7PVo8-2BxeSCeDL5jOu-2Bx5wws5UKOwmCQCTy6wc-2FTAihp-2FZilUgXpstXJftrsxyCzWfWHkMtlCi92uoep-2BB-2BEJJpbK-2BlDe4wqa-2FR0sOOAlwWz6aTEHqnEACadwVCrFtoPCBG68mO0yF5ItaBS0v1i7sukWtkhsoqWJbxt7FUowSScDsyM-3DExamining the email headers reveals that the phishing emails are sent using SendGrid’s infrastructure:
Received: from s.wfbtzhsv.outbound-mail.sendgrid.net (s.wfbtzhsv.outbound-mail.sendgrid.net [159.183.224.104])
(using TLSv1.3 with cipher TLS_AES_256_GCM_SHA384 (256/256 bits)
key-exchange X25519 server-signature ECDSA (P-384) server-digest SHA384)
(No client certificate requested)
by REDACTED (Postfix) with ESMTPS id 684BCE1862
for <REDACTED>; Tue, 12 Dec 2023 18:49:17 +0000 (UTC)SendGrid advertises an “industry-leading 99% delivery rate”. With even legitimate companies sometimes struggling to deliver emails to users’ inboxes successfully, it is easy to see how using SendGrid for phishing campaigns is attractive to criminals.
One giveaway indicates that the emails are not legitimate: while the campaign uses SendGrid’s email servers, the “From:” addresses do not use SendGrid’s domain name. Instead, the emails are sent from a variety of unrelated domain …